Bruger:Manscher/AES
AES
[redigér | rediger kildetekst]Development
[redigér | rediger kildetekst]Rijndael was a refinement of an earlier design by Daemen and Rijmen, Square; Square was a development from Shark.
Unlike its predecessor DES, Rijndael is a substitution-permutation network, not a Feistel network. AES is fast in both software and hardware, is relatively easy to implement, and requires little memory. As a new encryption standard, it is currently being deployed on a large scale.
Description of the cipher
[redigér | rediger kildetekst]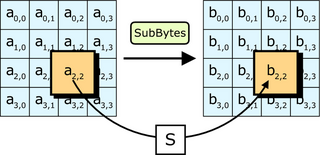 |
 |
 |
 |
Strictly speaking, AES is not precisely Rijndael (although in practice they are used interchangeably) as Rijndael supports a larger range of block and key sizes; AES has a fixed block size of 128 bits and a key size of 128, 192 or 256 bits, whereas Rijndael can be specified with key and block sizes in any multiple of 32 bits, with a minimum of 128 bits and a maximum of 256 bits.
The key is expanded using Rijndael's key schedule.
Most of AES' calculations are done in a special finite field.
AES operates on a 4×4 array of bytes, termed the state (versions of Rijndael with a larger block size have additional columns in the state). For encryption, each round of AES (except the last round) consists of four stages:
- SubBytes — a non-linear substitution step where each byte is replaced with another according to a lookup table.
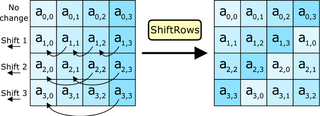
- ShiftRows — a transposition step where each row of the state is shifted cyclically a certain number of steps.
- MixColumns — a mixing operation which operates on the columns of the state, combining the four bytes in each column using a linear transformation.
- AddRoundKey — each byte of the state is combined with the round key; each round key is derived from the cipher key using a key schedule.
The final round omits the MixColumns stage.
The SubBytes step
[redigér | rediger kildetekst]In the SubBytes step, each byte in the array is updated using an 8-bit S-box. This operation provides the non-linearity in the cipher. The S-box used is derived from the inverse function over GF(28), known to have good non-linearity properties. To avoid attacks based on simple algebraic properties, the S-box is constructed by combining the inverse function with an invertible affine transformation. The S-box is also chosen to avoid any fixed points (and so is a derangement), and also any opposite fixed points.
The S-box is more fully described in the article Rijndael S-box.
The ShiftRows step
[redigér | rediger kildetekst]The ShiftRows step operates on the rows of the state; it cyclically shifts the bytes in each row by a certain offset. For AES, the first row is left unchanged. Each byte of the second row is shifted one to the left. Similarly, the third and fourth rows are shifted by offsets of two and three respectively. In this way, each column of the output state of the ShiftRows step is composed of bytes from each column of the input state. (Rijndael variants with a larger block size have slightly different offsets).
The MixColumns step
[redigér | rediger kildetekst]In the MixColumns step, the four bytes of each column of the state are combined using an invertible linear transformation. The MixColumns function takes four bytes as input and outputs four bytes, where each input byte affects all four output bytes. Together with ShiftRows, MixColumns provides diffusion in the cipher. Each column is treated as a polynomial over GF(28) and is then multiplied modulo with a fixed polynomial . The MixColumns step can also be viewed as a matrix multiply in Rijndael's finite field.
This process is described further in the article Rijndael mix columns.
The AddRoundKey step
[redigér | rediger kildetekst]In the AddRoundKey step, the subkey is combined with the state. For each round, a subkey is derived from the main key using the key schedule; each subkey is the same size as the state. The subkey is added by combining each byte of the state with the corresponding byte of the subkey using bitwise XOR.
Optimization of the cipher
[redigér | rediger kildetekst]On systems with 32-bit or larger words, it is possible to speed up execution of this cipher by converting the SubBytes, ShiftRows and MixColumns transformations into tables. One then has four 256-entry 32-bit tables, which utilizes a total of four kilobytes (4096 bytes) of memory--a kilobyte for each table. A round can now be done with 16 table lookups and 12 32-bit exclusive or operations, followed by four 32-bit exclusive or operations in the AddRoundKey step.
If the resulting four kilobyte table size is too large for a given target platform, the table lookup operation can be performed with a single 256-entry 32-bit table by the use of circular rotates.
Security
[redigér | rediger kildetekst]As of 2005, no successful attacks against AES have been recognised. The National Security Agency (NSA) reviewed all the AES finalists, including Rijndael, and stated that all of them were secure enough for US Government non-classified data. In June 2003, the US Government announced that AES may be used for classified information:
- "The design and strength of all key lengths of the AES algorithm (i.e., 128, 192 and 256) are sufficient to protect classified information up to the SECRET level. TOP SECRET information will require use of either the 192 or 256 key lengths. The implementation of AES in products intended to protect national security systems and/or information must be reviewed and certified by NSA prior to their acquisition and use." — [1]
This marks the first time that the public has had access to a cipher approved by NSA for TOP SECRET information. It is interesting to note that many public products use 128-bit secret keys by default; it is possible that NSA suspects a fundamental weakness in keys this short, or they may simply prefer a safety margin for top secret documents (which may require security decades into the future).
The most common way to attack block ciphers is to try various attacks on versions of the cipher with a reduced number of rounds. AES has 10 rounds for 128-bit keys, 12 rounds for 192-bit keys, and 14 rounds for 256-bit keys. As of 2005, the best known attacks are on 7 rounds for 128-bit keys, 8 rounds for 192-bit keys, and 9 rounds for 256-bit keys (Ferguson et al, 2000).
Some cryptographers worry about the security of AES. They feel that the margin between the number of rounds specified in the cipher and the best known attacks is too small for comfort. The risk is that some way to improve these attacks might be found and that, if so, the cipher could be broken. In this meaning, a cryptographic "break" is anything faster than an exhaustive search, so an attack against 128-bit key AES requiring 'only' 2120 operations would be considered a break even though it would be, now, quite infeasible. In practical application, any break of AES which is only this 'good' would be irrelevant. For the moment, such concerns can be ignored. The largest publically-known brute-force attack has been against a 64 bit RC5 key by distributed.net.
Another concern is the mathematical structure of AES. Unlike most other block ciphers, AES has a very neat mathematical description [2], [3]. This has not yet led to any attacks, but some researchers are worried that future attacks may find a way to exploit this structure.
In 2002, a theoretical attack, termed the "XSL attack", was announced by Nicolas Courtois and Josef Pieprzyk, showing a potential weakness in the AES algorithm. Several cryptography experts have found problems in the underlying mathematics of the proposed attack, suggesting that the authors may have made a mistake in their estimates. Whether this line of attack can be made to work against AES remains an open question. For the moment, the XSL attack against AES appears speculative; it is unlikely that anyone could carry out the current attack in practice.
In April 2005, D.J. Bernstein announced a cache timing attack that he used to break a custom server that used OpenSSL's AES encryption. The custom server was designed to give out as much timing information as possible, and the attack required over 200 million chosen plaintexts. Some say the attack is not practical against real-world implementations [4]; Bruce Schneier called the research a "nice timing attack." [5]


